
Today’s enterprises rely on increasingly complex digital platforms to deliver the essential services that businesses require. Whether it is converged communications platforms, client and sales systems or business critical operational platforms this digitally enabled infrastructure is at the core of delivering key business services.
The challenge this presents to businesses is not to just offer better availability and greater accessibility to stakeholders, but also to do this securely. However, with complexity and availability comes the threat of compromise and, regardless of the organisation, there will always be the potential for an organised crime gang or a disaffected/compromised employee to disrupt business operations.
Alongside that is the possibility of accidental (via phishing or malicious software) or mischievous damage to systems if the vulnerabilities that inevitably exist in the systems, and the way they are integrated, are not addressed.
In order to effectively target security activities, it is important to understand the holistic risks to any business and assess the interaction between people, process, and technology in the workplace. The Fortis Cyber Vulnerability Risk Assessment (CVRA) is an enterprise-wide risk assessment of an organisation’s current cyber security posture and awareness which highlights key threats and vulnerabilities so security activities can be effectively targeted and prioritised to mitigate risk.
Cyber Vulnerability Risk Assessment


Understand your current cyber security posture
Identify gaps, blind spots and potential threats
IASME Cyber Assurance
ISO/IEC 27001


WHAT ARE THE BENEFITS?
Optimise cyber resilience
Prioritise remediation activity
NIST Cyber Security Framework
US Department of Defense Cybersecurity Maturity Model Certification (CMMC)


The key benefits of undertaking a CVRA are to review existing security controls, understand the potential impact of
threats and vulnerabilities on business critical systems and assets and enable the organisation to take appropriate
action to adequately address any identified vulnerabilities.
Risk assessments are also a common compliance requirement for international security standards and security frameworks such as:
Address vulnerabilities and mitigate risk
Fortis has a proven pedigree in producing successful CVRAs that deliver significant and measurable business benefits. Our consultants are experts in their field and are National Cyber Security Centre (NCSC) Certified Cyber Professionals (CCP) and Security and Information Risk Advisor (SIRA) certified. They will work with you to tailor the CVRA to your organisation’s specific requirements and ensure it gets to the root of any identified risks, threats and vulnerabilities.
Our consultants gather vital information about the business and gain insight into current policies and procedures, analysing them against industry best practice, identifying gaps and highlighting areas to improve, resulting in a comprehensive and actionable risk assessment report and a recommended roadmap to remediate the outcomes.


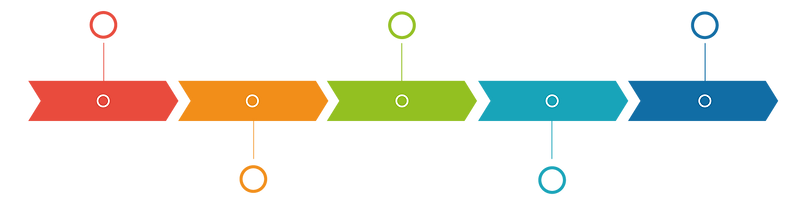
IDENTIFY
People, process, technology and how staff securely interact with technology
ASSESS
Risk assessment analysis process
Identify:
Our consultant will gather information about the organisation through documentation reviews and meetings and collate it into a set of preliminary models covering people, process, and technology. A vulnerability assessment will be undertaken to provide detailed evaluation of systems, and the threats and vulnerabilities against these systems.
Assess:
This is the analysis stage which will look at the physical, human, technical and social factors and their associated risks gathered from the identify stage.
REPORT
Mitigation plan and roadmap to de-risk in final CVRA report
Map:
Fortis will deliver a comprehensive security assessment covering security culture, technical and organisational security to identify common attack vectors and map against these discovered vulnerabilities.
Report:
Our consultant will produce a final report including a set of prioritised risks and recommended remediation activities and a summary visual maturity model that details the status of each risk.

MAP
Comprehensive security assessment of earlier phase outcomes

